Metasploit Vanish Sh Download Firefox
- Metasploit Vanish Sh Download Firefox Free
- Free Metasploit Download
- Metasploit Vanish Sh Download Firefox Download
This is the release log: Statistics:. Metasploit now ships with 635 exploit modules and 313 auxiliary modules. 47 new modules have been added since the last point release.
45 tickets were closed and 573 commits were made since the last point release. Metasploit is still about twice the size of the nearest Ruby application according to Ohloh.net (500K lines of Ruby) New Modules: New Exploits and Auxiliaries. Cisco Device HTTP Device Manager Access. Cisco IOS HTTP Unauthorized Administrative Access. Cisco IOS SNMP Configuration Grabber. SNMP Community Scanner.
Today we will be automating persistent backdoors on our target using metasploit framework. Lot's of fun!:D Introduction In an earlier video, we have seen how to craft an undetectable backdoor using the metasploit framework tools. Today, we are going to automate the process of sending such a backdoor to our victim(s) so.
Exim4. Bruteforce Capabilities:. Super-duper rservices commit (r11106). Big VNC update (r11033). Allow for blank FTP usernames.
(r10834). Add xampp default user/pass (r10936) Import / Export / Integration Capabilities:. Merge in nCircle support (r10902). Added the “ pwdump” format to dbexport. (r10862).
Updates to Nessus plugin (r11017). Added the ability to export hashes for John the Ripper (#3104) Web Crawling:.
New web crawler module (r10924, r11022). Moved Wmap crawler into a module.
Add the crawler mixin and a sample form extractor crawler (r11025). Move the crawler mixin to an auxiliary (r11026) General Updates & Changes:. Added PacketFu library. Properly show compatible payloads. Important for cross-platform exploits.
“The Social Engineering Toolkit (SET) is a python-driven suite of custom tools which solely focuses on attacking the human element of penetration testing. Rapid7 official statement regarding the incident: “ This morning the DNS settings for Rapid7.com and Metasploit.com were changed by a malicious third-party. We have taken action to address the issue and both sites are now locked down. We are currently investigating the situation, but it looks like the domain was hijacked via a spoofed change request faxed to Register.com.
We apologize for the service disruption, and do not anticipate any further implications for our users and customers at this time. We will keep everyone posted as we learn more, and let the community know if any action is needed.” Mirror of also available at. The incident, highlights a serious issue with how Register.com handles faxed change requests. Metasploit Pro, the commercial version of the product, now includes new PCI compliance reporting capabilities.
There is also a new Project Activity Report, which helps organization manage and track penetration testing activities. While there have been improvements to the commercial tool, open source users also benefit from some of the work done on Metasploit Pro 3.6 'The work behind the Pro Console actually resulted in major usability improvements to the standard Metasploit Framework console,' said HD Moore, chief security officer at Rapid7 and Metasploit's chief architect. 'All 64 of the new modules (including 15 exploits) are available in the open source version as well as the commercial products.' Changelog: - start msf button now kills msfrpcd session if dbconnect fails - set default database options to mysql with BackTrack 4 R2 settings. Armitage - Exit menu now kills msfrpcd, if the “Start MSF” button was used - Added ability to set up a multi/handler from Payload launch dialog Prerequisites to install Armitage. Armitage has the following prerequisites: - Java 1.6.0+ - Metasploit 3.5+ - A database and the information to connect to it Examples./msfrpcd -f -U msf -P test -t Basic Once you have a database, navigate to the folder containing the Armitage files and type:./armitage.sh Customizataion options You may edit these in the Armitage - Preferences menu. Ctrl Plus – zoom in - Ctrl Minus – zoom out - Ctrl 0 – reset the zoom level - Ctrl A – select all hosts - Escape – clear selection - Ctrl C – arrange hosts into a circle - Ctrl S – arrange hosts into a stack - Ctrl H – arrange hosts into a hierarchy.
This only works when a pivot is set up. Ctrl R – refresh hosts from the database Armitage will be a great tool for regular penetration testers. Who use open source tools hope in future Armitage also adds support for many other tools.
Download Armitage v11.25.10. Metasploit Framework 3.7.2 includes 698 exploit modules, 358 auxiliary modules, and 54 post modules, 11 new exploits, 1 new auxiliary module, and 15 new post modules.This release addresses several issues with updating the framework, adds 11 exploit / auxiliary modules and brings a plethora of new features. Modules included are listed below. Notable modules include the Cisco Anyconnect ActiveX bug (which works against recent versions of the Cisco AnyConnect Windows Client), and the SCADA modules by sinn3r and MC. The multi-platform post-exploitation work continues with new modules for Linux and Solaris included in this release thanks to Carlos Perez. A number of password-stealing post modules are also included, courtesy of David Maloney. The updates to the signedjavaapplet module are documented on the Metasploit Blog.
Additionally, the cachedump module has been improved and merged thanks to great work by Mubix. New features are equally exciting, including remote registry commands for Meterpreter, import parsers moved to nokogiri streaming parsers (for quicker parsing of large XML files), and updates to the egghunter payload to help the payload bypass DEP, thanks to Corelanc0der. See other notable improvements listed below. New Exploit Modules since 3.7.1. MS11-050 IE mshtml!CObjectElement Use After Free. AWStats Totals =.
In coordination with Metasploit Express and Metasploit Pro, version 3.6 of the Metasploit Framework is now available. Hot on the heels of 3.5.2, this release comes with 8 new exploits and 12 new auxiliaries. A whopping 10 of those new auxiliary modules are Chris John Riley's foray into SAP, giving you the ability to extract a range of information from servers' management consoles via the SOAP interface. This release fixes an annoying installer bug on Linux where Postgres would not automatically start on reboot. The feature I am most excited about is the new Post Exploitation support. I hinted at this new module type in the 3.5.2 release announcement and with 3.6, more than 20 new modules are available. Post modules are a new, more powerful, replacement for meterpreter scripts.
Scripts were clearly tied to a single platform: meterpreter for Windows. With modules it is much easier to abstract common tasks into libraries for any platform that can expose a session. For example, file operations are common across all platforms - windows/meterpreter, windows/shell, linux/shell, etc. Post modules can simply include Post::File and have access to platform-agnostic methods for interacting with the file system. In the near future, this sort of abstraction will be extended to Windows registry manipulation and service control.
Too much generality can make it difficult to access OS-level features and when you really need to get down and dirty with a session, you still can. Post modules have a Session object exactly as meterpreter scripts did and you can still access all of the low-level methods available to it. That means you can use railgun for performing complex system manipulation (ie. Smartlocker) when necessary. A major benefit of Post modules is the ability to easily include other mixins from the framework. From a user's perspective, this means more consistent reporting and option handling than are currently available with scripts.
This also opens the door to local exploits for a variety of platforms, including Windows, Linux, and even Cisco IOS through SSH and Telnet sessions. Although post modules are meant to replace meterpreter scripts, scripts are not going away any time soon. We understand that many users still rely on private scripts for their post-exploitation needs and porting all of them to the new format will take time.
So while we will be favoring module contributions over scripts, that doesn't mean your private code is suddenly going to stop working. This is an exciting release. As always, it is immediately available from the. At DEFCON 20, Raphael Mudge the developer of Armitage released the most significant update to Armitage. Armitage is now fully scriptable and capable of hosting bots in acollaborative hacking engagement.
Raphael Mudge is the founder of Strategic Cyber LLC, a Washington, DC based company that creates software for red teams. He created Armitage for Metasploit, the Sleep programming language, and the IRC client jIRCii. Previously, Raphael worked as a security researcher for the US Air Force, a penetration tester, and he even invented a grammar checker that was sold to Automattic. Armitage is a graphical cyber attack management tool for Metasploit that visualizes your targets, recommends exploits, and exposes the advanced capabilities of the framework. Armitage aims to make Metasploit usable for security practitioners who understand hacking but don’t use Metasploit every day.
If you want to learn Metasploit and grow into the advanced features, Armitage can help you. This is the official change log:. Fixed a race condition causing some file browser actions to fail on Windows hosts at times. Files downloaded through file browser are now archived in: hostDownloads.
Hail Mary output nows goes to log dirallhailmary.log. Added Crack Passwords button to Credentials tab. This opens the launcher for John the Ripper: auxiliary/analyze/jtrcrackfast.
Added Post Modules item to Meterpreter N - Explore and Shell N menus. This menu item will show applicable post-exploitation modules in the module browser. Loot browser now opens loot viewer as a tab. Loot viewer now has many of the same keyboard shortcuts as a console tab.
You can Ctrl+F to search for stuff, Ctrl+Plus/Minus to increase and shrink the font, and Ctrl+A to select everything. Statistics. Metasploit now ships with 687 exploit modules, 357 auxiliary modules, and 39 post modules. 2 new exploits and 2 new auxiliary modules have been added since the last release. Highlights & New Features This release address a performance issue with HTTP Services and adds a few modules.
In addition, a bug in the Windows auto-update task has been corrected, along with minor changes to the Windows installer. New Modules. VideoLAN VLC ModPlug ReadS3M Stack Buffer Overflow. ICONICS WebHMI ActiveX Buffer Overflow.
SPlayer 3.7 Content-Type Buffer Overflow. OpenSSL. This is the official change log:.
Major performance improvements. Major system refactoring and code clean-up. Major module API refactoring providing even more flexibility regarding element auditing and manipulation. Integration with the Metasploit Framework via: ( New). ArachniMetareport, an Arachni report specifically designed to provide WebApp context to the Metasploit framework. Arachni plug-in for the Metasploit framework, used to load the ArachniMetareport in order to provide advanced automated and manual exploitation of WebApp vulnerabilities.
Advanced generic WebApp exploit modules for the Metasploit framework, utilized either manually or automatically by the Arachni MSF plug-in. Improved Blind SQL Injection module, significantly less requests per audit. XMLRPC server ( New). XMLRPC CLI client ( New).
NTLM authentication support ( New). Support for path extractor modules for the Spider ( New). Path extractors: ( New). Generic — extracts URLs from arbitrary text. Anchors. Form actions. Frame sources.
Links. META refresh. Script ‘src’ and script code. Sitemap. Plug-in support — allowing the framework to be extended with virtually any functionality ( New). Added plug-ins: ( New).
Passive proxy. Automated login. Added modules: ( New).
Audit. XPath injection. LDAP injection. Recon. CVS/SVN user disclosure. Private IP address disclosure.
Robot file reader (in the Common Files module). XST.
WebDAV detection. Allowed HTTP methods. Credit card number disclosure. HTTP PUT support. Extended proxy support (SOCKS4, SOCKS4A, SOCKS5, HTTP/1.1 and HTTP/1.0). ( New) This release adds many improvements, optimizations, new features and components. We have new modules, plug-in support, modular path extractors for the Spider, XMLRPC Client/Server interfaces and probably more stuff I’m currently incapable of recalling.
The new plug-in functionality has been used to implement a passive proxy and an automated login plug-in allowing for scripted, form based, authentication. Using the passive proxy you can selectively choose the pages you want to audit by browsing them, login to the web- application and enable Arachni to audit AJAX based web pages by allowing it to see what your browser sees. The AutoLogin plug-in enables the framework to log-in to a given web application before the scanning process starts and alleviates the need to go through the hassle of creating and setting your own cookie-jar. The new XMLRPC services allow for remote and distributed –agent-like– deployment of Arachni.
Download Arachni v0.2.1 ( arachni-v0.2.1.tar.gz). A 7-year-old critical remote code execution vulnerability has been discovered in Samba networking software that could allow a remote attacker to take control of an affected Linux and Unix machines. Samba is open-source software (re-implementation of SMB networking protocol) that runs on the majority of operating systems available today, including Windows, Linux, UNIX, IBM System 390, and OpenVMS. Samba allows non-Windows operating systems, like GNU/Linux or Mac OS X, to share network shared folders, files, and printers with Windows operating system. The newly discovered remote code execution vulnerability affects all versions newer than Samba 3.5.0 that was released on March 1, 2010. 'All versions of Samba from 3.5.0 onwards are vulnerable to a remote code execution vulnerability, allowing a malicious client to upload a shared library to a writable share, and then cause the server to load and execute it,' Samba wrote in an published Wednesday. Linux version of EternalBlue Exploit?
According to the Shodan computer search engine, more than 485,000 Samba-enabled computers exposed port 445 on the Internet, and according to researchers at, more than 104,000 internet-exposed endpoints appeared to be running vulnerable versions of Samba, out of which 92,000 are running unsupported versions of Samba. Since Samba is the SMB protocol implemented on Linux and UNIX systems, so some experts are saying it is 'Linux version of,' used by the.or should I say SambaCry? Keeping in mind the number of vulnerable systems and ease of exploiting this vulnerability, the Samba flaw could be exploited at large scale with wormable capabilities. Home networks with network-attached storage (NAS) devices could also be vulnerable to this flaw. Exploit Code Released! (Bonus: Metasploit Module).
The flaw actually resided in the way Samba handled shared libraries. A remote attacker could use this Samba arbitrary module loading vulnerability to upload a shared library to a writable share and then cause the server to load and execute malicious code. The vulnerability is hell easy to exploit.
Just one line of code is required to execute malicious code on the affected system. Simple.createpipe('/path/to/target.so') However, the Samba exploit has already been ported to, a penetration testing framework, enabling researchers as well as hackers to exploit this flaw easily. Patch and Mitigations The maintainers of Samba has in their new versions Samba versions 4.6.4/4.5.10/4.4.14, and are urging those using a vulnerable version of Samba to install the patch as soon as possible. But if you can not upgrade to the latest versions of Samba immediately, you can work around the vulnerability by adding the following line to your Samba configuration file smb.conf: nt pipe support = no Once added, restart the network's SMB daemon (smbd) and you are done. This change will prevent clients from fully accessing some network machines, as well as disable some expected functions for connected Windows systems.
While Linux distribution vendors, including Red Hat and Ubuntu, have already released patched versions for its users, the larger risk is that from NAS device consumers that might not be updated as quickly. Craig Williams of Cisco said that given the fact that most NAS devices run Samba and have very valuable data, the vulnerability 'has potential to be the first large-scale Linux ransomware worm.' Update: Samba maintainers have also for older and unsupported versions of Samba. Meanwhile, Netgear released a for CVE-2017-7494, saying a large number of its routers and NAS product models are affected by the flaw because they use Samba version 3.5.0 or later. However, the company currently released firmware fixes for only. Runs on Linux kernel 4.0,. use full Gnome 3 Desktop instead of gnome-fallback,.
improved hardware and wireless driver coverage,. support for a variety of Desktop Environments,. updated desktop environment and tools,. Featuring new cutting-edge wireless penetration tools,. Kali Linux now added desktop notifications, so that you do not miss anything,. Support Ruby 2.0, which will make Metasploit will load much faster,.
Kali 2.0 added inbuilt screencasting tool so that you can record desktop. Another parameter 'isadmin' can be manipulated to 'Yes' value that allows the attacker to self-elevate to administrative privileges in the web application itself. 'The fact that a static session encryption key is in use across all instances of the NAS means that once a user has a valid session cookie on one instance, they can apply that same cookie directly to another instance and acquire the same level of access. In short, once a user is logged in as admin on one instance, they’re effectively admin on every instance,' Reeves explained in an advisory. Connects to the vulnerable NAS device and extracts a cisession cookie. Decrypts the cookie using the static encryption key and extracts the PHP hash.
Modifies the serialized PHP hash so that the username is set to 'admin' and the isadmin field is set to 'yes'. Encrypts this updated PHP hash ready for further use as a cisession cookie, which allows future requests to operate on the NAS as if they were an administrator. Performs a request to extract the host configuration, which includes the device's description. Modifies the host configuration so that the device description contains a small stager payload. Performs a request to update the host configuration with the new data so that the stager payload is written to /etc/devicedesc. Modifies the PHP hash again so that the language parameter contains the value././././etc/devicedesc x00. Encrypts this new PHP hash ready for future use as a cisession cookie.
Performs a request to the NAS using the cookie created in the previous step, which invokes the stager that was written to disk. This request posts a larger payload which is written to disk under the web server root. Performs another request which then resets the host configuration back to what it was prior to exploitation. In UXSS attacks, client-side vulnerabilities are exploited in a web browser or browser extensions to generate an XSS condition, which allows the malicious code to be executed, bypassing or disabling the security protection mechanisms in the web browser. ' Users of these platforms may also have installed vulnerable aftermarket browsers,' Beardsley explains in a on Tuesday. ' Until the Google Play store XFO X-Frame-Options gap is mitigated, users of these web applications who habitually sign in to their Google Account will remain vulnerable.'
. First, the module exploits a Universal Cross-Site Scripting (UXSS) vulnerability present in versions of Android's open source stock browser (the AOSP Browser) as well as some other browsers, prior to 4.4 (KitKat). Second, the Google Play store's web interface fails to enforce a X-Frame-Options: DENY header on some error pages, and therefore, can be targeted for script injection. As a result, this leads to remote code execution through Google Play's remote installation feature, as any application available on the Google Play store can be installed and launched on the user's device. The Android bug has been called a ' privacy disaster' by Tod Beardsley, a developer for the security toolkit, and in order to explain you why, he has promised to post a video that is ' sufficiently shocking.' “ By malforming a javascript: URL handler with a prepended null byte, the AOSP, or Android Open Source Platform (AOSP) Browser) fails to enforce the Same-Origin Policy (SOP) browser security control,” Tod Beardsley of Rapid7 said in a. ' What this means is any arbitrary website - say, one controlled by a spammer or a spy - can peek into the contents of any other web page,' Beardsley said.
' If you went to an attackers site while you had your webmail open in another window, the attacker could scrape your email data and see what your browser sees.” ' Worse, he could snag a copy of your session cookie and hijack your session completely, and read and write webmail on your behalf.' Polish Computer Emergency Response Team (CERT Polska) recently a large scale cyber attack ongoing campaign aimed at Polish e-banking users. Cyber criminals are using known router vulnerability which allow attackers to change the router's DNS configuration remotely so they can lure users to fake bank websites or can perform Man-in-the-Middle attack. ' After DNS servers settings are changed on a router, all queries from inside the network are forwarded to rogue servers. Obviously the platform of a client device is not an issue, as there is no need for the attackers to install any malicious software at all.'
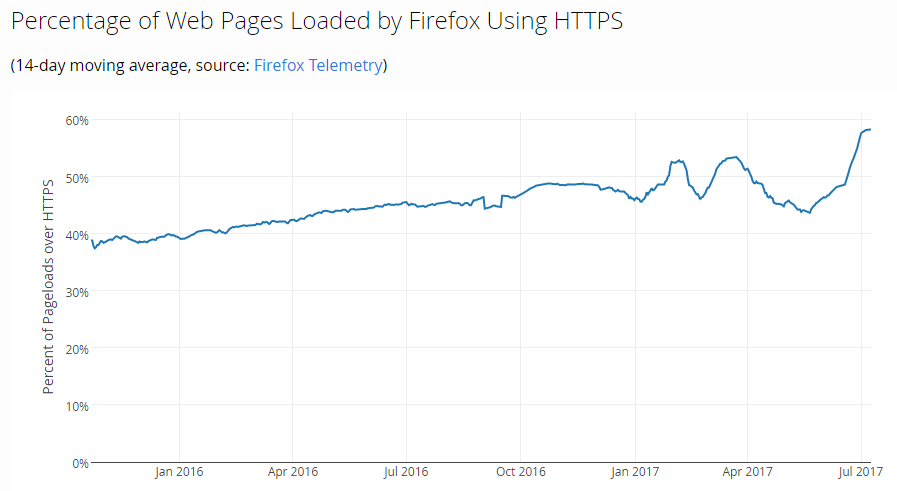
CERT Polska researchers said. That DNS Hijacking trick is not new, neither most of the router vulnerabilities are, but still millions of routers are not patched or upgraded to the latest firmware version. The Domain Name System, or DNS, the Internet’s method of converting Web page names into IP address numbers can be hijacked just by changing the server address to a malicious DNS server from router's settings; and that which malicious DNS server should be in control of the hacker to facilitate interception, inspection and modification of the traffic between users and the online banking websites they wanted to target. ' It looks like criminals are primarily targeting e-banking users as they modify DNS responses for several banking domains, while resolving other domain names normally.' Most of the Banking and E-commerce sites are using HTTPS with SSL encryption, making it impossible to impersonate them without a valid digital certificate issued by a Certificate Authority (CA), but to bypass such limitation cyber criminals are also using the SSL strip technique to spoof digital certificates. “ While criminals intercept the unencrypted request, they simply modify links to clear HTTP, adding “ ssl-“ String to a hostname, apparently in an attempt to fool casual users (Note that the nonexistent ssl.
Hostnames would only be resolved by malicious DNS servers) While the connection is proxied through malicious servers, SSL is terminated before it reaches the user. Decrypted content is then modified and sent unencrypted to the customer.” ' In cases we have seen, they produced a self-signed certificate for thawte.com domain, which causes a browser to complain about both domain name mismatch and lack of a trusted CA in the certificate chain. This should be a clear indicator of the fraud for most users.'
Our readers can get detailed explanations of exploitation technique on the Nassereddine's blog. How to Protect? Now that you know how hackers can target routers to mess up the internet connection or even steal banking, Facebook, Google passwords, the next best thing to do is to secure your own routers:.
Change the default username and password. Update the Router's firmware to latest patched version. Users can spot fake sites by pay attention to the browser’s address bar and HTTPS indicators. Disable Remote Administration feature, especially from WAN. The router should be configurable only from the local network or LAN. ' If there ever was a book that should not be judged by its title, Defense against the Black Arts: How Hackers Do What They Do and How to Protect against It, is that book.
Even if one uses the definition in The New Hackers Dictionary of 'a collection of arcane, unpublished, and (by implication) mostly ad-hoc techniques developed for a particular application or systems area', that really does not describe this book. The truth is that hacking is none of the above. If anything, it is a process that is far from mysterious, but rather aether to describe. With that, the book does a good job of providing the reader with the information needed to run a large set of hacking tools.' Ben's review.
If you are yet unaware, Microsoft pushed out another couple of security updates this month and in their new “Microsoft Vulnerability Research and Defense” blog. Msoft started it a couple of weeks ago, providing lower level technical information about the vulnerabilities they are fixing. Be sure to install if you haven’t already. The first of the updates, MS08-001, provides reason for caution, because it allows for reliable exploitation.
Surprisingly, we have not seen any public exploitation or even PoC just yet. You can watch a by the makers of Bindiff, a binary diffing tool used to uncover security vulnerabilities like this one. Grab your popcorn, bring a date, and head on over. I’ll ruin the ending for youof the nine functions changed in the tcpip component that was patched, they examine one function that iterates a list of structures and mistakenly performs a bad comparison. They even find some overwriteable memory for successful exploit! One of the highest hitting worms that ThreatFire encountered over the past week is a worm designed to target online game player logins by dropping a password stealer and rootkit components on infected systems. We about the that drops rkd.dll, amvo0.dll and amvo.exe, and now we observe many more variants that are repacked with some fairly sophisticated packer and code perversion technology.
Metasploit Vanish Sh Download Firefox Free
The password stealers themselves are updated on various websites that we have observed moving locations throughout China, repacked for AV and emulation evasion purposes. We also see ongoing with the dropper. The executables all display very unusual static PE characteristics. First, the import directory contains the name of one dll (kernel32) and imports only three of its functions (LoadLibraryA, GetProcAddress, ExitProcess), the bare bones minimum that you need for a PE packer: All of the section names are mangled, to further raise our suspicion: And finally, the resource section is huge and unrecognizable to a simple resource section parser (hint — it contains more executable code): Unfortunately, effectively this incessant rate of change results in a low rate of AV scanner detection: If you are seeing a popup like this one, go ahead and quarantine the thing. Yesterday, we were further analyzing an executable that we recently haven’t been seeing all that much of, tmpms45.exe. The filename is familiar, as sometimes various executables with that name are delivered by malicious emails or malicious web pages.
Most often, we see it as a part of a commodity exploit kit (i.e. ), and the malicious web site operators simply forgot to change the filename in the kit’s scripts that they just purchased. This time, however, a file delivered with that filename is receiving a lot of attention as the newest piece of malware writing directly to raw disk and the on WindowsXP systems. It may also go by several other names, like mat16.exe, mat17.exe, mat18.exe and so on. The code for the malicious itself is getting attention partly because it is the first in the wild malware found to contain a slightly modifed version of the “BootRoot” code presented at by eEye researchers.
This malicious dropper executable is being distributed from web sites via a set of exploits targeting a vulnerability patched in 2003, the common Microsoft MDAC (MS06-014) vulnerabilities that we see targeted on a daily basis, along with the somewhat more recent VML and XML CoreServices BoF. As predicted in an, the slow cooker has been heating it up. Several years of the Fbi’s efforts are related to botnets and cybercrime. Eleven people are indicted in this case, involving spam and a “pump and dump” scheme for thinly traded Chinese penny stocks: “The charges arose after a three-year investigation – led by agents from the Federal Bureau of Investigation, with assistance from the U.S. Postal Inspection Service and the Internal Revenue Service – revealed a sophisticated and extensive spamming operation that, as alleged in the indictment, largely focused on running a stock “pump and dump” scheme, whereby the defendants sent spam touting thinly traded Chinese penny stocks, drove up their stock price, and reaped profits by selling the stock at artificially inflated prices.” The fraudulent spam messages were sent off of zombies around the world. Keep those bots off of your Windows systems. Eight of those individuals charged are being sought, including a Peter Severa of Russia.
This individual is one of the longest running spam operators on the internet. You can see a description of this individual on: “ One of the longest operating criminal spam-lords on the internet.
Works with many other Easter Euro and US based botnet spammers.” Maybe, just maybe, there will be a day when this sort of garbage doesn’t show up in my email:. “Add Enerbrite tech to your Radar Volume spike today, big news expected this week Symbol: E-T-G-U Currently: $ 0.0017 Big News is due out this week and trading volume is off the charts. People are loading up.
Read the latest PR and find out what they know. You’ll want to get in on ETGU too. Dont miss this chance to ride a multibagger.
Add ETGU to your Radar and get in MONDAY before the news gets out. “There is no real excellence in all this world Which can be separated from right living.” David Star Jordan”. We are seeing a number of hits from binaries served up from the Ukraine via web pages’ prompts from domains registered in China and hosted in the U.S.
Now that’s international. These sites in the Ukraine are linked to by servers all over the world, and serve up “Rogueware”, or fraudulent adware, similar to the Zlob family. A couple of vendors are assigning it vague family names like “Delflob” or “Delf”. Through a redirected http session, the user sees the standard video codec hoax. Recently, this same hoax coldly was used with other shocking news like the Bhutto assassination and the, and most likely will continue to be used throughout 2008.
This site could have been a part of the effort, but because detection is so low, it is most likely a new effort or will be a part of a new effort. Notice the “play video” title bar and the instruction “You must download the Video ActiveX Object to play”: Once the user is suckered into clicking on the image to download the adware posing as a legitimate video codec, a file with variations on the name installvideo3913230.exe is served up. If the user runs the installer, thinking of it as a legitimate codec, it in turn writes out G76-tmp.exe, which also installs toprates.dll. Toprates.dll is a file that claims to be a video driver in its properties, but it is nothing more than rogueware (also called rogue antispyware), or adware making fraudulent and threatening claims that a user’s system is infected and in a dangerous state. And by paying up, the user will soon fix this dangerous situation.
ThreatFire users have been seeing prompts regarding the temp file’s (%TEMP% GL76-tmp.exe) adjustments to security settings: If the user allows the action to occur and then double clicks on “My Computer”, or opens an explorer window another way, they are prompted with an intimidating warning. In yesterday’s, I mentioned that the ChaseNET forums have been shut down. The distribution links for their SharK project, Bifrost and Poison Ivy Rat (Trojan) suites also have been removed. These projects could arguably be described as “Remote Administration Tools”. Monday, the British legislature published for the application of a that makes it illegal to distribute “hacking tools”. A perfect example of tools that this new application might apply to would be the ChaseNET projects.
While these RATs could be argued as tools comparable to PCAnywhere or GoToMyPC, they include stealth and information stealing functionality that is designed to evade security solutions for effective system compromise, control and theft of sensitive user data. These sorts of tools certainly fit under the description of “dual-use” tools, and I suppose the British law was developed with the intent to take down this sort of site. We’ll take a look from a low level technical perspective at some of these RATs’ bad behaviors and provide some details in a later post. AV veteran Peter Ferrie of Symantec noticed that the he has been fighting for so long has been winding down. The scene’s virus writers are beginning to post their farewellz and shoutz on the 29A forums and others. He also points out that the trojan scene has steadily been replacing the activity of vx writers: “We are striving to put them out of business. Once they’re all gone, those Trojans will keep us in business for a long time.
Not that we want them, either.” Even those trojan groups are beginning to disappear. The ChaseNET forums, a major international source of “Remote Administration Tool” (RAT for short, otherwise known as “Trojan Horse”) activity since 2004, are closing down as well. This shutdown curiously coincides with the Fbi arrest of longtime ChaseNET member “Digerati”.
He faces up to five years in prison and a $250,000 fine if convicted of conspiracy to commit computer fraud, as we last year. While the oldest of the groups might be drying up, unfortunately there are more growing to replace the vxers in different parts of the world.
Recently released “Zines” from these newer groups publish technically sophisticated source details of password stealing, advanced rootkitting techniques, and more. These zines follow the trend away from virus writing for reputation to password stealer writing for profit. Plug in the slow cooker, cuz we’ll see more “” style arrests in 2008. Unfortunately, we are also seeing more posts overseas from individuals seeking bot herding partners, looking to install more adware on victims’ systems and raise revenues for those involved. This sort of collaboration and malware should also continue throughout 2008, as we have been seeing a high level of this activity at the end of 2007. Some of the most prevalent malware ThreatFire currently is seeing comes from the families that are distributed in this manner. And here is one of the requests that we are seeing on an overseas forum regarding rogueware installs: “ We upload adware, which in turn actively advertises antispyware!
Our adware does not conflict with the botnets, or trojans, and it does not affect your own bots.” Update: Bot Roast II resulted in. This time from Gregory King, indicted at the same time as “Digerati”.
His deal includes a two year prison term. In a, I presented steps for unpacking and restoring the IT/IAT of a suspicious BHO for analysis purposes. In that case, it was packed with a tool called “Upack”, otherwise known as the “Ultimate PE Packer” by its author Dwing. Upack often is used on executable files around 40kb in size. It compresses the file’s contents with the LZMA algorithm and adds an unpacking stub to the target file for self-decompressing at runtime. In other words, to make a file smaller for download and delivery without requiring a decompression utility like WinZip or WinRar to already be installed on another system at runtime, an author can compress their executable creation with this tool. This posting will work with the PE file that was recreated from that previous work.
A was started on the DailyDave mail list by Dave himself, criticizing information warfare papers: “If you’re reading an information warfare book or paper you’ll invariably see a lot of: 1. Inane references to Sun Tzu (or, in some even more horrible cases, any two of Sun Tzu, Clausewitz, and John Boyd) 2. Declarations that information warfare is an “asymmetric attack” Dave goes on to drop a couple product names and then describe the money saving mono-culture Microsoft technology implementations within the US.com and.mil communities, and describes it as poor strategy: “Bad strategies like this result in flailing and moaning as you get defeated over and over by someone with better strategy, not because the battlefield is inherently asymmetric.” Unfortunately, according to a couple of groups. (Although, I’m not sure that statement is completely true. It seems more to have been a record year for reporting breaches, due to a number of new factors. Incident reporting has always provided only a cloudy window into actual events.) Any way you slice it, in light of the sheer volume of security breaches, Dave’s statement about the mono-culture of.com and.mil communities is a troubling one — in spite of a year of record profits for the.com community and record budgets for the.mil community, it seems that technology implementations still are not getting the budget or focus that they require when it comes to effectively addressing security needs. Another poster on the list responded to Dave’s complaints about “Spec Ops: Case Studies in Special Operations Warfare: Theory and Practice” by William McRaven, a U.S.
Navy SEAL commanding officer. I got a chance to check it out this past week and the eight case studies McRaven analyzes really are fascinating (if you’re a bit of a military history buff). The theory and principles at the beginning of the book (summarized on the DailyDave post) can be applied to analysis of the targeted attacks that have become much more commonplace on the net. It’s a stimulating read for security enthusiasts, and applies well to the ongoing security breaches around the world: “If you can’t draw the parallels to general security practices from those principles then the book is not for you, otherwise you might find yourself ripping through the book and thinking in an entirely different light by the final chapter.”. What a generous way to bring in the new year.
Free Metasploit Download
The Storm/Peacomm gang, the same group whose activities we at VB2007 and, has not disappeared. The holidays brought a round of Christmas-themed spam, complete with a simple link to a njinx servers and the promise of a friendly xmas related message. In the past couple of days, they have turned towards a new year theme: “Happy New Year! Your download should begin shortly. If your download does not start in approximately 15 seconds, you can click here to launch the download and then press Run.
Enjoy!” Consistent with their past attacks, the executable name is themed as well. We have seen “happynewyear2008.exe”, “happy2008.exe” located on servers in Poland and multiple sites around the world. But in a small departure from using just unregistered ip addresses, these malware serving web hosts are now registered with cute, related DNS.com domains, like “newyearwithluv” or “hellosanta”. The gang broke another trend and flashy graphics on the sites are not present either.
We are seeing a strong uptick in the number of users actually running these files (happy-2008.exe, happynewyear2008.exe, happy2008.exe, happy2008.exe, happynewyear.exe) on their systems. Please exercise caution when visiting links that were sent to you, update all of your system patches at the Microsoft Update site, and if using Quicktime or Firefox, update them as well. Cheers to secure computing and happy New Year! With one of the corniest titles you’ll see , the Kaspersky blog in Russia stated that the original authors of the Pinch trojan have been arrested: “Today Nikolay Patrushev, head of the Federal Security Services, announced the results of the measures taken to combat cyber crime in 2007. Among other information, it was announced that it had been established who was the author of the notorious Pinch Trojan – two Russian virus writers called Ermishkin and Farkhutdinov. The investigation will soon be completed and taken to court.” Maybe this focus by the Federal Security Services helps explain some of the motivations for the Russian Business Network’s moves to China and Central America. The arrest themselves are a pretty big deal, along the lines of the more recent Zotob author’s and distributor’s arrests.
According to the KAV log: “ The arrest of the Pinch authors is on a level with the arrests of other well known virus writers such as the author of NetSky and Sasser, and the authors of the Chernobyl and Melissa viruses.” Interestingly, it seems that the author of the Pinch code and the distributors that use it to infect millions of computers are different people. Here is another take on the announcement: “FSB Chief, Patrushev, reported that FSB has arrested Ermishkin and Farkhutdinov, who created and deployed the Pinch trojan into tens of millions of PCs around the world.” The assembly source that I’ve seen from version 1.0 contains a different name, “Alex”. The two recently arrested most likely used the code to create and infect systems, and most likely were not the original author. We’ll look for corrections in reports. Joining the bandwagon of future tellers, Cisco recently read the collective palm of malcode writers and cybercriminals everywhere and released what they saw in their. Seriously though, the report takes perspective on some pretty massive themes and is a worthwhile read for security managers and other interested users.
It provides “an overview of the combined security intelligence of the entire Cisco organization”, which is an interesting statement in itself, knowing that the company has over 60,000 full time employees and lots of contracted and outsourced staff. I like its structure and layout, but you’ll still find a lot of questionable statements in its details, so end users might be pretty well confused by some of the key statements. Malware activity gets stuffed under the Vulnerability section. Their crystal ball tells us What to Expect in 2008, partly based on what they have not seen in the past (disregarding the golden rule that absence of evidence is not evidence of absence in the security arena): “More malware may execute in system memory, not on hard drives.” Huh?
I can’t remember the last time a piece of malware, or any code for that matter, executed on the hard drive, instead of in the CPU and memory. And what about caching or paging? Ok, we can get past that statement. The point seems to be that “more” malcode may run on systems without ever touching users’ hard drives: “Malware attacking rootkits that executed entirely in system memory emerged in 2007. As average RAM size continues to increase in the coming year, these strategies will likely grow in popularity”. Imho, not exactly.
These strategies have been around for a long time in the underground and cybercriminal coding communities, but it hasn’t been a money maker — Aphex’s downloader circa 1999 is an example. The key feature was that it downloaded any content to memory from a remote location (like a web server) and executed the content in memory without the content ever touching the disk. I am sure his was not the first, but he was one of the first from the shadier side of the underground to develop and publicly release a reliable loading technique like this one on his website. The downloader, and its scanner evasion techniques, just weren’t needed at the time. Problems from using the technique had nothing to do with the size of physical memory on the victim system. But there were easier methods of detection evasion.
Kinda confusing. Anyways, enough of my nitpicking, it is an interesting read with a fine list of key recommendations, predictions, and some exposure to their collected data from 2007. I’ll get through more of the malware section and update this post with notes about what I really like in the report. In a previous post, I mentioned that we could use to analyze some shellcode currently being posted in the wild by malicious web site operators. These malicious websites are delivering malware by exploiting several Windows based vulnerabilities. The websites attack visitors by targeting vulnerabilities in, and in the QuickTime plugin. In our labs, we visit these web sites with vulnerable systems, allowing the pages to compromise the systems.
We then analyze the techniques being used. Let’s take a quick look at a major part of the attack — the shellcode within the delivered malformed wmf file. We’ll take a look at the low level data content of the malformed file itself: After seeing a lot of these malformed files, you can spot the shellcode right away. I did in the above image after a quick visual scan, but sometimes details of the file format need to be known to find the shellcode on the first try.
We copy out the string of shellcode hex data into a c-style string, like this one: “ x83 xec x10 xd9 xee xd9 x74 x24 xf4 x58 x33 xc9 xb1 xdb” I copy it into the buffer in the c file from the, and the assignment will look like this: unsigned char shellcode = “ x83 xec x10 xd9 xee xd9 x74 x24 xf4 x58 x33 xc9 xb1” I compile it using gcc, but you can use the cl.exe Microsoft compiler if you would like — whatever c compiler should be fine. Ncaa softball umpire mechanics manual. I’ve never seen a problem with substituting one for another: C: sh gcc sh3ll.c -o sh3ll.exe The compiler emits an expected warning that can be ignored, and now we have an executable to work with. We’ll run it in Olly to its entry point, and then search for the beginning of the shellcode string in memory. When we find it, we’ll set a memory access break point on that memory location and then let the process run to that point by hitting f9. When the debugger arrives at this starting point for the shellcode, the debugger shows us a very strange listing — “jno” instruction followed by a bunch of “cnq” instructions?
The listing looks very strange: We hit f7 a few times and notice “xor byte ptr ds:eax+12, 99″, followed by a loopd instruction that takes us back to a few lines prior. This loop is an xor decoder loop, implemented in this shellcode because we are exploiting BoF, and usually that means we are attacking a string handling flaw. Any “00″ or null bytes in the code will likely, as explained in chaps 3, 7, 9.
We also notice that ecx is set to “0xdbh” at 0040200e, meaning that this loop will decode the subsequent 219 bytes of data: We can continue stepping through the code with f7, watching the decoding taking place, until ecx decrements to zero. When it finishes, we step through a bit more slowly. Stepping into the instructions with f7 now reveals the code searching for kernel32′s location in the process space using the common and reliable technique of parsing the PEB and its module initialization linked lists.
It then searches for LoadLibraryA, ExitThread, and WinExec win32 api calls. It loads urlmon and finds URLDownloadToFileA.
These calls all tell us that this shellcode’s functionality is download and execute — and we can observe the url strings that the code is communicating with. Download and execute shellcode like this happens to be some of the most prevalent shellcode that we see served up by malicious web sites. Hope that you learned a few things about the sorts of techniques we can use to analyze shellcode and its behaviors. Let me know what you think of it! Ok, this one is a bit late, but I don’t stop by the Merriam Webster dictionary every day: We have heard the w00ting that goes along with 0day and additional exploit releases from around the world — it’s been tossed around by the haxor crowd for years. You can get a hold of metasploit exploit developers y0 and mc. D4rkgr3y from and m00 security even named his PoC release code “m00-apache-w00t.c” back in 2003.
Defcon monitors, alongside, are filled with the stuff every year in Vegas. A Linksys hack a VMware virtual machine escape technique (see if you can find the w00t!). An entire family has been crawling around the internet.
Wezzer they suxxored or not, Merriam Webster just might pwn all you n00bs next year. I’m guessing we’ll see a lot less of this lingo in the underground chat rooms and forums now. Interestingly, #2 on the list was ““, another sexy term and hangout for all the l337 kidz.
While the may be known for high tech research like analytical chemistry, neutron science, and providing technology and expertise to support national and homeland security needs, they also might become known for a recent. Granted, the only data they are reporting as having been compromised is their visitors database. “Oak Ridge National Laboratory (ORNL) recently experienced a sophisticated cyber attack that appears to be part of a coordinated attempt to gain access to computer networks at numerous laboratories and other institutions across the country.
A hacker illegally gained access to ORNL computers by sending staff e-mails that appeared to be official legitimate communications. When the employees opened the attachment or accessed an embedded link, the hacker planted a program on the employees’ computers that enabled the hacker to copy and retrieve information. The original e-mail and first potential corruption occurred on October 29, 2007. We have reason to believe that data was stolen from a database used for visitors to the Laboratory.” Targeted attacks like this one are more common than they were a couple of years ago. Be wary of incoming email attachments and hyperlinks. UPDATE : Speaking of data breaches and network intrusion, has a related on his blog today about a newly released study. The UC Berkeley Samuelson Law, Technology, & Public Policy Clinic recently completed and released a study on ““.
It evaluates the profound effects on practices within U.S. Companies resulting from the implementation of security breach notification state laws.
We are seeing a strong surge in the spread of a game password-stealing worm. A number of reports online have described the infection occurring when the user was copying files over a usb drive. The files that we are seeing drop an executable in the windows system32 directory by varying names: “avpo.exe” and “niedeiect.com” are common. This nasty little thing copies itself to various locations on your drive, drops driver files possessing unstable rootkit techniques to hide its own files, and steals the passwords of your favorite games. If you see “avpo” or “amvo0.exe” performing strange behaviors alongside “niedeiect.com” on your drive, like writing to the explorer.exe process, quarantine them.
Dave Aitel, founder of, sometimes comments on and Sabre security (oops, I mean zynamics) projects. They speak at a lot of the same conferences.
He just happened to be flying back from jfk when a few deep thoughts came to mind about evading the holy grail of that he posted on: “Given that avoiding “behavioral signatures” is a matter of calling random NOP-like API calls (i.e. CreateFile + CloseHandle 1 NOP), Halvar’s program classification techniques involve a structural differencing engine. This has advantages (see his talk for details) in that program structure closely reflects the semantic meaning of a program, as interpreted by a compiler.
So the obvious way, from what I can tell, to defeat a structural differencing algorithm would be to do a static or dynamic analysis of your target program, and for each CALL opcode, change the destination to a dispatcher function. This dispatcher function can then be built to do a O(1) table lookup to find the true destination of the call.” I like the way Dave thinks. Unfortunately, other folks do too, and all sorts of evasive techniques are commercially available. That means the techniques are available to the bot herders, and it appears in our labs that the herders are distributing most of their bots packed with this stuff now. That went by the aliases Akill and Digerati were arrested by the fbi and New Zealand authorities. “The FBI estimates that more than one million computers have been infected and puts the combined economic losses at more than $20 million.” The arrests are a part of the Fbi’s ongoing ‘‘.
The arrest and past behavior of the Penn State student Ryan Brett Goldstein that went by the handle “Digerati” also is being discussed on the underground forums where he shared advice and code since around 2000. Rumors surrounding his bot herding and bot update techniques, his activities of accidental university server DoS attacks, and intentional DDoS’ing groups of other underground coders continue to circulate.
Metasploit Vanish Sh Download Firefox Download
Update: Bot Roast II resulted in. This time from Gregory King, indicted at the same time as “Digerati”.
His deal includes a two year prison term. The folks at spamhouse.org have done a commendable job over the years trying to make the internet a better place for everyone.
They provide interesting weekly statistics and information on the world’s worst Spam Kings and sources of spam in general. If you’re a network admin, you’ve heard of these guys. Over the past year, while malicious servers continue to be set up all over the world, more activity is taking place in China. The servers that were a part of the recent google poisoning that we looked at first were in located in China. Many of the redirected pages from other compromised servers link to exploit pages, downloaders and more malware served in China. Not surprisingly, this week China is the number two source of spam, (keep in mind that these numbers do change on their site): But of their weekly top, the top 6 continue to be Russian or Ukranian.
Only two are of Hong Kong or Chinese origin: Also along those lines, the whole or RBN (a huge network well known for its malicious activity over the past few years), was tracked by iDefense as shutting down and from and. And from what we are seeing at our user base and in our labs, it looks like this trend is one that will continue. UPDATE : The Sydney Morning Herald published a (it appears to be from someone at The Guardian) this morning about the RBN network’s activities. Fyi, this writeup is geared to satisfy curiosities about technical stuff, to start responding to some of the interest expressed over at our. You have been warned We use for all sorts of things around here.
It’s an outstanding tool. In fact, Olly himself found some spare time and is releasing a new version soon. He’s got the pre-alpha version 2 code available on his website. His debugger is a very useful tool for reversing user-mode software.
When we’re looking to get to the bottom of a suspicious component, one way is to fire up olly and get started. Unfortunately, there are challenges to that approach. Sometimes, we need to understand what a dll or other component is doing as well, and sometimes those dlls and other components are packed. In yesterday’s post, we noted that the Sans 2007 Top 20 list contains some obvious trends away from OS components targeted by network worms and more towards third party components. Is a casualty in that direction. CSA is Cisco’s host-based security product (it would be installed on your system like any other piece of software) that makes for a juicy remote exploit target because it’s remotely accessible.
This vulnerability, unfortunately, also leads further down the path of complexity and into the kernel: “A buffer overflow vulnerability exists in a system driver used by the Cisco Security Agent for Microsoft Windows. This buffer overflow can be exploited remotely and causes corruption of kernel memory, which leads to a Windows stop error (blue screen) or to arbitrary code execution.”. An about China’s cyberattacks on British businesses from MI5: “The Government has openly accused China of carrying out state-sponsored espionage against vital parts of Britain’s economy, including the computer systems of big banks and financial services firms.” It interestingly came out a week after from the blasted the PRC’s espionage activities: “Chinese espionage in the United States, which now comprises the single greatest threat to U.S.
Technology, is straining the U.S. Counterintelligence establishment.” The report also discusses the PRC’s DDoS capabilites and cyberwarfare capabilities. The word “cyber” appears over thirty times in that report, in relation to “attacks”, “weapons” and “warfare”.
While the usual yearly predictions are coming out from large av scanner vendors, here’s an containing an ex-CIA official’s statements on how many attacks occurred against the federal government in 2007 alone. The numbers are staggering, when considering it’s only one year of successful criminal activity: “America is under widespread attack in cyberspace,” Palowitch said in citing Cartwright’s statistics that there were 37,000 reported breaches of government and private systems in fiscal 2007. There were nearly 13,000 direct assaults on federal agencies then, and 80,000 attempted computer network attacks on Defense Department systems, he added. A long list of porn sites currently are attacking recent quicktime and some other older browser side vulnerabilities. Unfortunately, it looks like some of our users are getting hit with this stuff in the wild — these exploits and malware are prevalent. It looks as though the purpose is to download, install, and run a service that acts as a trojan clicker.
Clickers like this one continue to fetch web pages from related porn sites and their banner ad links in the background, without the user noticing (although your network card and cpu might appear to be pretty busy!). This activity turns into revenue for the individuals hosting the sites that the clickers are fetching pages from.
Here is what an infected system with the installed service looks like. Monday morning, Adam Thomas of the Sunbelt crew to use the information from a shocking news story about the death of a girl to lure in new rogueware IeDefender victims. While we haven’t seen a large spike in the downloads of this stuff, we’ve been monitoring the site — it remains up. In our lab, we saw closely related but slightly different results. The videomp3setup.exe file, when manually run, pops a couple of different and changing windows: Following the rogueware install, the software will open an Internet Explorer window, conveniently googling the term “sex” for you, and injecting its own html into the results, spoofing the google results. The first chunk of injected HTML is a warning posing as though it is from google: “Google Error!
Your computer is infected!” The second chunk immediately follows the fraudulent claim. It inserts a pornographic image next to a phony link that claims to be on the youtube site (clicking on it directs you to a completely different porn domain, not youtube). You can see the (censored) fraudulent results here: Unfortunately, scanner results seemed to be spotty to non-existent for this threat: We’ve distributed samples to the appropriate people for inclusion in other security products’ protection.